
We all know that cyber risk is a feature of our world that is unlikely to disappear. However, how many of us have really thought about it in any depth? What would happen if our treasury data was maliciously corrupted or amended? What effect could that have on our ability to manage financial risks and settle our corporate obligations? Mark Carney, governor of the Bank of England, is worried enough about it to have identified a catastrophic cyberattack as one of the top four risks that could potentially trigger the next financial crisis. In this article we will explore why it is particularly relevant to treasurers, what you can (and cannot) do to manage the risk, and why insurance is not the answer. But before we head into those points, it may be helpful for you to familiarise yourself with some common types of cyber fraud via our handy terminology guide… 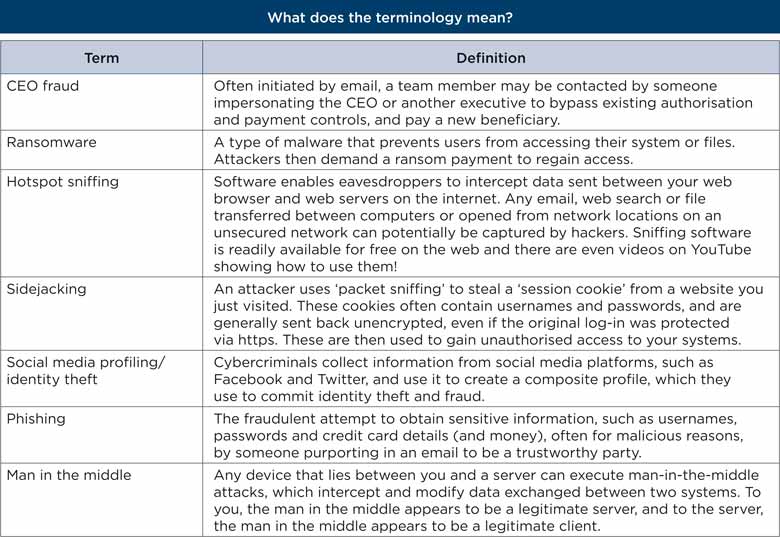
We’re all busy people and as treasurers we have a responsibility for managing financial risks for our organisations. We don’t worry too much about firewalls (unless they stop us doing our job) and expect our IT team to protect our technology infrastructure. However, if we ask the right question, we may be unlucky enough to find that our IT teams are focusing on company-wide applications and have assumed that the treasury team looks after its own specialist software. It is these third-party applications that can sometimes present the greatest risk to the organisation (as Target Corporation found to its cost in a pivotal attack in part brought about through vulnerabilities in the way the retailer connected to third-party vendors). Has anyone looked at the vulnerabilities at the intersection between internal networks and these applications? Has your legal team understood your responsibilities and liabilities as data moves across your network and those of third parties? If it turns out that safeguarding specialist treasury applications is the responsibility of the treasury team, we often hear that this is an area too complex and expensive to deal with. However, as the treasurer of a FTSE 20 company mentioned recently, a breach “will happen to us at some point” – and we have no choice but to be prepared.
Whether we are specifically targeted by fraudsters or affected by an attack on a wide range of organisations, as with a distributed denial of service attack, for example, changes to, or loss of, our data can have serious consequences for our business. At the very least, it can distract us from normal activities as we seek to restore the integrity of our systems and data. At the very worst, we may initially be unaware of the fact that our data has been compromised and miss interest payments or currency exposures with all of the serious repercussions that can potentially entail.
We may initially be unaware of the fact that our data has been compromised
Banks have invested significant sums to protect us from hacks into our payment systems through data encryption, transaction authentication, dual-key access and so on. However, we need to ensure the integrity of these key controls and understand how they could potentially be compromised if we’re using mobile devices in public wi-fi locations to process payments, for example (see hotspot sniffing and sidejacking in the above terminology table). It’s not just the corrupted data that cybercrime can expose us to. Our reputations are also at risk. After all, no one wants to appear on the front pages. While it’s probably right to rely on the CIO, can you afford to damage your internal reputation and the reputation of your treasury team?
Ideally, we should encourage the IT department to take ownership of the treasury department’s IT infrastructure. This would consolidate the risks, effort and skills in one team. If this proves impossible, we should at least follow any internal guidance on managing cyber risk, including dealing with CEO fraud, ransomware, phishing and man-in-the-middle attacks. The best way to prepare for an attack is to create a ‘what to do in the event of a cyberattack’ plan and then test it.
Cybersecurity is a responsibility for all of us – do not assume your IT team is looking after all your applications
A cyberattack is probably not like anything you’ve faced before and requires a change in mindset. I’ve been lucky enough to witness a cyberattack ‘war game’ and I was surprised how people responded when they felt under attack. Normal protocols (such as not sharing passwords) fell away, demonstrating how weak operating controls can be when put under pressure. This highlights how many of the risks stem not from technology, but simply from human behaviour. Whether it’s opening an unusual attachment or providing the IP address for a market news server to a stranger, it is often our human curiosity or desire to be helpful that lets us down.
In our brave new world, cybersecurity is a responsibility for all of us – do not assume your IT team is looking after all your applications. If you’re unlucky enough to experience a breach, ensure you have a clear mitigation plan in place. We know treasury is all about risk management – in a way, this is no different.
Find further high-quality cybersecurity information and tips via these links:
City of London Police cybercrime advice and support EACT CyberSecurity Working Group Bank of England, HM Treasury and the Financial Conduct Authority (guidance on making sure the UK financial sector runs smoothly, efficiently and effectively) The UK National Cyber Security Centre
Insurance – guidance and advice on what’s available Augmented risk in a digital world (see page 22 of this PDF download) HSBC/Celent – Combatting Treasury Fraud Cyber Fraud – the Impact on Treasury, by Bellin How to address cyber vulnerabilities in corporate treasury 2018 AFP Risk Survey – key findings Deutsche Bank Roundtable: Treasury Executives Can Lead the Way in Cyber
Naresh Aggarwal is associate director in the ACT’s policy & technical team This article was taken from The Treasurer magazine. For more great insights, log in to view the full issue or sign up for eAffiliate membership
