
Fifty years ago, before the advent of always-connected banking, staff in branches would be able to recognise and authenticate customers and their signatures. Knowing your customers was something bank employees were required to do.
Now, with the rapid move away from physical branches to electronic communications, e-banking and mobile apps, authentication has also had to keep pace.
As we start to move to fully electronic transactions, including FX, payments, finance and trade, the method by which we prove who we are is being strengthened, both as consumers and employees.
We currently have less direct, physical interaction with bank staff than ever, proving that you are indeed an authorised person requesting bank services is essential.
No doubt treasury staff will be familiar with the drawer full of security tokens – each issued by a different bank, sometimes for a subset of accounts – by which the electronic banking system is secured.
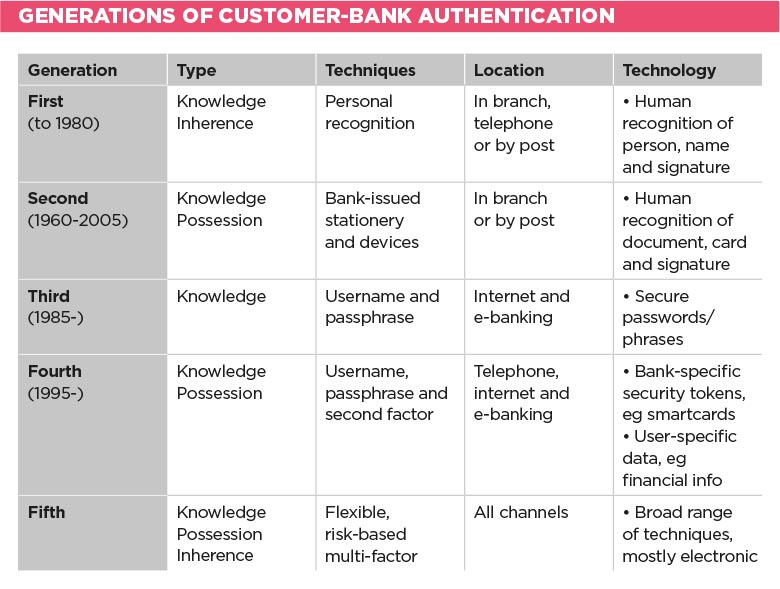
This is the fifth generation of customer authentication and goes hand in hand with improved KYC and anti-money-laundering requirements placed on the banking industry.
The key driver behind this is the evolving nature of crime. Today, most financial crime is electronic, with the criminals located perhaps in a different country from the bank.
There is a goal to increase competition in the services used by treasury and consumer
Defrauding businesses and consumers by misusing weak security measures has become the norm and initiatives such as secure, chip-based payment cards have now rolled out worldwide, with the US one of the last adopters.
In addition, there is a goal to increase competition in the services used by treasury and consumer. Fintechs are looking to leverage bank data and services to provide improved, end-to-end solutions across banks that can solve problems for a subset of the client base.
Better supply chain finance, integrated directly with payables and enterprise resource planning systems, is one such example. The name for this initiative is Open Banking and is encoded in the EU’s second payment services directive (PSD2), but the quid pro quo is adoption of strong customer authentication, so banks can be sure it is their customer transacting.
What PSD2 says is that the payment service user must be authenticated by their payment service provider under three situations:
These three cover pretty much every case in which corporates use banking services, from change of mandates to e-banking, download of statements and, of course, issuance of credentials. It’s likely that businesses will see authentication pop up more frequently in their engagements with the bank, including over the telephone.
PSD2 also states that some part of the authentication should be dynamic, ie not relying on static data, such as a password, but transaction- or time-based one-time codes or response to security challenges.
In the UK, we are familiar with the last method in the context of PINsentry devices, which generate an eight-digit code based on online banking transaction information. These will become more prevalent.
Banks are looking to minimise the impact on the customer experience and some authentication could be done transparently, for example, voice recognition on telephone banking and device recognition of your usual laptop when using online banking.
It is certain, however, that there will be some change, and corporates should prepare to adopt these new technologies as they roll out over the next 18 months.
So, what are the implications for treasury?
First, in the EU, it is likely that your bank may want to introduce new methods of proving who you are as an employee of their client. This is likely to mean that new security tokens may be issued and you may be asked to register your voice so the bank can be sure it’s you when you call them.
This will apply to anyone who deals with your bank, in many cases not just treasury staff, but those in payments factories and senior management in group companies.
Second, authentication is likely to become more personal. While you can share a security token with a colleague, even if against bank advice, it is much more difficult to share a biometric. Banks will correlate use of tokens with biometrics, so don’t get them mixed up between users, as if you do, you could get temporarily locked out.
Third, some banks are trialling mobile-based authentication, such as fingerprint, voice or ‘selfie’. While your work phone may be capable of handling these needs, many users will choose to use their own phones for convenience.
This opens up the potential that a significant payment from a company may be authorised on a device that isn’t owned by it and may not have appropriate security measures. Already there are cases of apps available from the Google Play Store that have malware hidden inside and are targeted to compromise bank apps, such as authentication and mobile banking.
Fourth, each bank will select its own technology and techniques for authentication, which may cause confusion and add to the requirements on internal IT security. This may mean that systems that access the bank, but can be managed centrally, such as a payments gateway, may become preferable in terms of cost of ownership.
Lastly, under the EU’s forthcoming General Data Protection Regulation, which becomes enforceable on 25 May 2018, biometric data must be treated as sensitive personal information, so storing this on a bank server or a work mobile for business purposes, such as bank authentication, will bring it into the scope of corporate compliance.
The political goal of opening up the customer-to-bank interface for all customers, corporate and consumer, is common across Europe and is starting to gain traction in North America. To secure these new, electronic portals to the bank, security must be improved to protect customers’ accounts and assets from financial crime.
While authentication has moved forward, criminals have moved quickly, too, and corporates risk being at the tail end of the initiative to reinforce banking infrastructures. Corporates would be best advised to embrace the change as soon as possible.
Some of these are static, such as passwords, and some dynamic, such as facial images.
Use of more than one of these types of authentication method improves confidence that the individual is the same one who registered, but in most cases not directly their identity.
Some of these give a weak correlation with identity, such as location, and others are much stronger, such as one-time cryptographic codes.
Jonathan Williams is an adviser on payments, identity and fraud prevention at Mk2 Consulting.
This article was taken from the June 2017 issue of The Treasurer magazine. For more great insights, log in to view the full issue or sign up for eAffiliate membership
